Blog about the latest in Mobile Commerce, Mobile Devices, Mobile Security and Social Media.
Wednesday, February 19, 2014
Sunday, February 16, 2014
Top 23 African Start-Ups 2014
The Top 23 African Start-Ups in 2014 Are:
- The Able Wireless Company aims to stream paid-for content for $6 per month using a household set-top box. It is an edge-of-network service that ‘delivers content over a wireless network through a secure device, reducing 83% of capital and operational costs for current network providers, creating a legitimate distribution system
- Karibu Solar Power The Karibu solar system is a small standing lamp, that is split into three components: the lamp, the battery and the small solar panel. The merchant ‘rents’ out the lamp and battery for a few weeks, before the renter owns the whole device, including the charger. Using the same small amounts that are typically used to buy kerosene, Karibu provides light but also power to charge cellphones READ MORE
Labels:
2014,
Africa,
Ecommerce,
education,
environment,
Mobile Apps,
Start-Up,
StartUp,
Technology
Thursday, February 13, 2014
The Common Myths Of Unlimited Bandwidth Offers
courtesy of www.insidedevices.org
In the world of today access to the internet is a bare necessity for anyone. Most of us own multiple devices that require Internet access (Laptops, Desktops, Smartphone, Tablets, Fablets etc.) We are all looking to connect those and want to have the fastest connection available. So what do we do? We look for a company (ISP) offering us the best internet package. All of us start looking for a package that is cheap and offers the maximum speed and data transfer rates commonly known as bandwidth. Broadband means a transfer rate of 256Kbit/s or higher. To conclude: an Internet connection with a larger bandwidth can move a set amount of data (say, a video file) much faster than an Internet connection with a lower bandwidth, hence the broad(er)band connection.
Does Unlimited Bandwidth Exist?
Well, it is real when you look at the marketing strategies of various web hosting service providers across the world, but in reality there is nothing called unlimited bandwidth. It is always limited, either by data cable, internet or network card.
What?! Yes Think about it!
Bandwidth is not free! READ MORE
Labels:
2014,
Devices,
Ecommerce,
Internet,
internet of things,
Mobile Marketing,
Mobile Phone,
Online Selling
Sunday, February 9, 2014
Monday, February 3, 2014
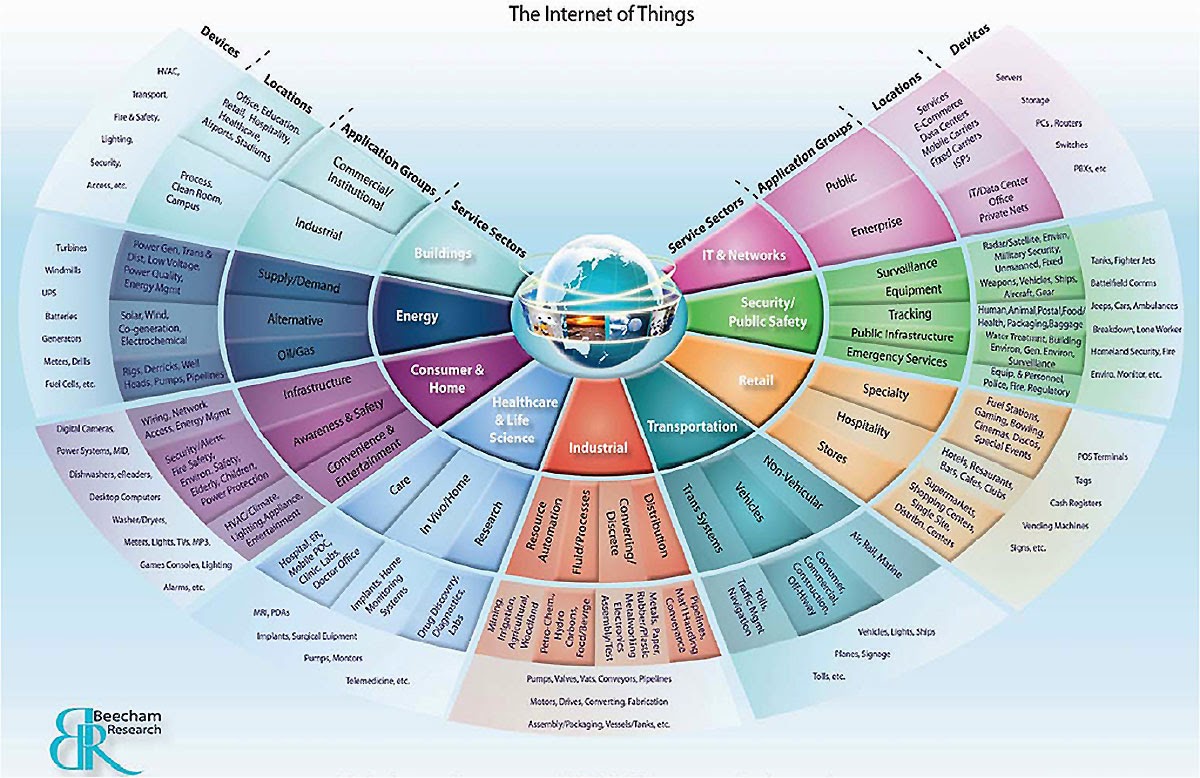
IoT: 2 Alternative Network Communication Channels for Cloud
The startup FizzJelly is offering cellular-connected devices for monitoring a range of sensors. These are hobbyist devices, intended for experimenters and developers to create their own IoT systems. The systems are Arduino-compatible and fully open for experimentation and customization.
So far, this sounds like many other IoT offerings. What is different about this start up, is its method for connecting with the user. There is no mobile app or web service associated with FizzJelly. Instead, it uses (SMS) messaging for information exchange. This makes the system compatible with more than 80% of all mobile phones (smart or otherwise) now deployed. Talk about penetration rate!
1. TEXT Messaging (SMS) It is important to understand that the various sensors you establish in your network work READ MORE -->
Sunday, February 2, 2014
IoT: Top 5 M2M Key Challenges for 2014 and beyond
The Internet of Things (IoT) is based on the implementation, integration and use of Machine-to-Machine (M2M)Communication powered by the Internet. The philosophy is basic and for the IoT to succeed; the relationship device/machine-internet-end user has to be integrated. The reality however is very different. Major standards development organizations, including the ETSI, agreed on a common M2M service layer, oneM2M, in January 2012 as part of a global initiative to drive M2M standardization, two years down the line, progress has been made but not on the scale hoped for.
Top 5 M2M Key Challenges For 2014 And Beyond
- Ecosystem: The ecosystem faces numerous implementation challenges.Existing M2M solutions are highly fragmented and dedicated only to singular applications, as a result it will slow down the development of the Global M2M Market.
- Interoperability & Capability: READ MORE
Labels:
2014,
Capability,
Devices,
IoT,
M2M,
Mobile Devices,
www.insidedevices.org
Saturday, February 1, 2014
IoT: The Philosophy of the Net is Dead
"The problem that we now face is that the internet into which IoT is being born is philosophically very different to the internet into which the web was born."
Internet vs. IoT: A Closer Look at Key Philosophies
The Internet of twenty-plus years ago and prior was a place of free love and open standards.Coming from academia where commercial pressures were low, we moved into the era where internet connectivity onto PCs was the norm --The introduction of Windows 95 -- The way we as a society put the internet to use, has had an uneasy relationship with this "free love", uncommercial philosophy. Think back on how we us get our hands on any type of material ( , studies, music, video etc) for free. In line with the academic philosophy and its influence on the net that information should be freely available for anybody who took an interest in it. For the information producers it was a challenging time as some commercial realism had to be added.
The Internet Of Things (IoT) uses the internet READ MORE
Labels:
Android,
Ecommerce,
Internet,
internet of things,
IOS,
IoT,
Mobile Devices
Friday, January 31, 2014
Internet of Things: BotNets exist. ThingBots do not
Does “ThingBot” excist? [----> Read More]
Thursday, January 30, 2014
How To Protect Your Smartphone or Tablet in 2014
until 2011 PC's and Laptops where mainly targeted by virusses. Until then Mobile devices have flown under the threat radar with PCs mainly taking the abuse. As a result, many smartphone and tablet owners give little thought to the risks that lurk behind deceivingly harmless apps.
It's not a surprise that smartphones and tablets are no safer from invasions than computers. A digital device is a digital device, regardless of its size and portability. Nonetheless there are a number of ways you can protect your phone or tablet (DO) and there are a number of things you should be aware (DON'T) which I will list below:
READ MORE: HERE
READ MORE: HERE
Wednesday, January 29, 2014
The Internet of Things: Top 5 Device Security Tips VISIT
blog courtesy of www.insidedevices.org
Gates’ could control about anything in his house by the tap of his finger, whilst driving his car 20 miles away from his house.
Welcome to the “The Internet of Things“(IoT) that does represent a revolution happening right now. All kind of companies – not just technology and telecommunications firms – are linking “things” as diverse as smartphones, cars and household appliances to industrial-strength sensors, each other and the internet. The technical result may be simple features such as intercommunication and autonomous machine-to-machine (M2M) data transfer, but the potential benefits to lifestyles and businesses are unprecedented.
Ofcourse there is a “But”….with great opportunity comes great responsibility. Along with its conveniences, the IoT will be exposed to unprecedented security challenges: data privacy, safety, governance and trust.
What Are The Main Security Loopholes?
Security loopholes can occur anywhere in the IoT; but you can devide into two groups:
Data Risks: all smart devices will transmit data to a storage point before (in most cases) a bulk upload to the provider, often with outdate security settings.
Privacy Risks: all our smart devices collect, aggregate and transmit our user data, even tiny items of data in aggregate can identify, define, and label you without your knowledge.
What Can You Do To Protect Your Data and Privacy?
- Audit the devices you own.
- Secure your device. If a device is connected to your network, it means that it is potentially accessible over the internet.
- Verify the security settings on any device you purchase. If it is remotely accessible, disable this feature if it isn’t required
- Change any default passwords to something only you know. A long combination of letters, numbers and symbols will generate a strong password.
- Check the manufacturer’s website to see if there are updates to the device’s software. If security vulnerabilities are discovered, manufacturers will often patch them in new updates to the software. PATCHING IS EVERYTHING
What Is The Best Example Day-To-Day Example of A Device That Poses A Risk To Our Data and Privacy?
Read the full article here
Sunday, April 28, 2013
4 Ways To Increase Password Security for SMB's
 |
| gigaom.com |
While establishing a password policy and educating workers are good first steps, they are not sufficient to convince users to select good passwords.
SMBs frequently inherit their employees' selection of passwords, and while three-quarters of workers choose passwords for security, they also compromise to more efficiently gain access to their accounts.
"A business is only as strong as its weakest link, or weakest password connected to that business, whether belonging to a customer, partner or employee," CSID stated in the report.
Here are 4 Ways for businesses to increase password security
 |
| Mozakdesign.com |
SMBs generally have no idea the strength of the passwords that their employees are using on internal systems, whether they are reusing the passwords on external services or how many different passwords they have. The first step for businesses to gain visibility should be to adopt a central system for managing employees credentials, whether a password-management service in the cloud or full identity and access management (IAM) solution.
Without such a system, companies will be blind as to the degree of risk they have, LastPass's Siegrist says.
"The scary thing is that most people don't know any better, so if you don't have any tools or procedures in place, you just have no shot of getting to a safe place," he says.
"The scary thing is that most people don't know any better, so if you don't have any tools or procedures in place, you just have no shot of getting to a safe place," he says.
LastPass for instance, gives each employee's account a security score based on their currently stored passwords. While company administrators cannot access the passwords themselves, they can discover when a worker is not following policy.
Even for companies that do not need a full IAM system, the centralized management of employees' passwords goes beyond just gaining insight into workers' password habits. Companies that have administrative control over their employees' accounts can add new workers and delete old ones who no longer work at the firm, heading off the risk from disgruntled employees.
"As companies grow, even to 50 or 100 users, tracking where they've added users have added accounts into different applications not only becomes a burdensome process, but can also become expensive," says Patrick Harding, chief technology officer of Ping Identity, a cloud identity provider.
Ping's product eliminates passwords for many cloud applications by using a single sign-on approach that replaces passwords with Security Assertion Markup Language (SAML) to securely access online accounts.
 |
| Liebsoft.com |
In addition to centralizing the administration of the identity storage, companies can benefit from simplifying a user's need to enter in a credential to a single login event. By limiting the number of times a user has to enter in a password, companies can make their workers more efficient and focus on a single channel to secure, Harding says.
"If you only have to authenticate once a day, make that authentication stronger than a password, even a strong password," he says.
Using two-factor authentication for an e-mail account can double as the log-in credentials for the single sign-on system.
4. Change employee behavior
Finally, companies should use any improvements in their management of passwords to educate them about good passwords selection, LastPass's Siegrist says. When employees reuse a password, remind them of company policy against reuse. If workers have not updated old passwords, then remind them to do so, he says.
Finally, companies should use any improvements in their management of passwords to educate them about good passwords selection, LastPass's Siegrist says. When employees reuse a password, remind them of company policy against reuse. If workers have not updated old passwords, then remind them to do so, he says.
"You can set policies to perfectly customize how safe you want your employees to be, and know that they are doing it,"Siegrist says.
Labels:
Cloud,
Data Security,
Password,
Security,
Small Medium Business
Thursday, April 18, 2013
Top 6 BYOD Risks
In my last post I discussed the top Benefits of BYOD and ended with the promise to discuss the main risks or concerns associated with BYOD. Before I do; it is important to understand that new technologies such as the enterprise cloud, cloud-based apps, social media, and high-powered mobile devices offer more ways to access corporate data.
1. Data Management, segregation for compliance reasons
Many financial regulators or auditors require certain sensitive data to be adequately protected and stored with documented evidence to prove. With Cloud and Mobility this can prove a challenging equation. Key Challenge will remain the assurance and evidence although IT/Security Departments should be provided with a clear guideline on data management policies or devices (3rd party included) on which data is stored
2. (Unknown) 3rd Party Access via Mobile Apps
When employees download and install their personal apps on their personal device, they allow unregulated third-party access to other sensitive, corporate information stored on their devices. Additionally Wi-Fi Access points could potentially access corporate data.
3. Data Tracking (Nightmare)
The ability to track and manage corporate data has become more difficult with the adoption of new technologies like Cloud and Mobile Storage Services in the Enterprise. Organization are often not equipped to track data effectively and need to rely on 3rd party providers and rely on employees to follow the guidelines.
4. Lost or Stolen Devices:
A simple truth is that PC's or even Laptops do not go missing that easily as a smartphone or tablet, due to the sheer size. The risk is in the fact that Mobile Devices in general are either not password protected or lack a robust protection. An additional factor of risk is corporate espionage via deliberate targeting of device.
5. Employees leaving
Employees leaving a company "forget" to inform HR of their own device containing corporate information. Unhappy employees can leak information to competitors.
Most of this can be mitigated fairly easy by reminding HR teams and employees that any corporate data either stored on mobile devices or cloud service remains owned by the company. Termination or Exit Policies are almost in all companies common practice
6. Additional Cost instead of Savings
Many CEO's view BYOD Policy as an easy cost-saver, however to manage and monitor points 1,2,3 and 5 (point 4 is ambiguous) new IT policies, hardware and employees need to brought into place which is likely to be more costly as the graph indicates.
The picture here is not as black and white though as the graphs below will demonstrate
After spending a lot of time on BYOD researching it I am still not sure whether the benefits (at this time) outweigh the risks involved. I can see the immense potential and benefits for both employers and employees but am still uncomfortable with the complexity and possible security and policy gaps.
1. Data Management, segregation for compliance reasons
Many financial regulators or auditors require certain sensitive data to be adequately protected and stored with documented evidence to prove. With Cloud and Mobility this can prove a challenging equation. Key Challenge will remain the assurance and evidence although IT/Security Departments should be provided with a clear guideline on data management policies or devices (3rd party included) on which data is stored
2. (Unknown) 3rd Party Access via Mobile Apps
When employees download and install their personal apps on their personal device, they allow unregulated third-party access to other sensitive, corporate information stored on their devices. Additionally Wi-Fi Access points could potentially access corporate data.
3. Data Tracking (Nightmare)
The ability to track and manage corporate data has become more difficult with the adoption of new technologies like Cloud and Mobile Storage Services in the Enterprise. Organization are often not equipped to track data effectively and need to rely on 3rd party providers and rely on employees to follow the guidelines.
4. Lost or Stolen Devices:
A simple truth is that PC's or even Laptops do not go missing that easily as a smartphone or tablet, due to the sheer size. The risk is in the fact that Mobile Devices in general are either not password protected or lack a robust protection. An additional factor of risk is corporate espionage via deliberate targeting of device.
5. Employees leaving
Employees leaving a company "forget" to inform HR of their own device containing corporate information. Unhappy employees can leak information to competitors.
Most of this can be mitigated fairly easy by reminding HR teams and employees that any corporate data either stored on mobile devices or cloud service remains owned by the company. Termination or Exit Policies are almost in all companies common practice
6. Additional Cost instead of Savings
Many CEO's view BYOD Policy as an easy cost-saver, however to manage and monitor points 1,2,3 and 5 (point 4 is ambiguous) new IT policies, hardware and employees need to brought into place which is likely to be more costly as the graph indicates.
The picture here is not as black and white though as the graphs below will demonstrate
After spending a lot of time on BYOD researching it I am still not sure whether the benefits (at this time) outweigh the risks involved. I can see the immense potential and benefits for both employers and employees but am still uncomfortable with the complexity and possible security and policy gaps.
Labels:
BYOD,
Data Management,
Employees,
Employers,
Helpdesk,
HR,
IT Department,
Mobile Apps,
Risks,
Stolen Devices
Thursday, April 11, 2013
Top 5 Benefits of BYOD
The latest trend in a lot of public and private organizations is the allow employees to use their personal devices for work purposes.
In this blog I am going to list the 5 main benefits.
Here we go!
1. EMPLOYEE REQUESTS:
The most obvious benefit to embracing BYOD is employee engagement and retention. If you are in an industry full of creatives, Gen-Y or tech savvy employees, it's a no brainer and you probably had BYOD before we all came up with the catchy label. Giving employees choice and respecting different preferences can demonstrate progressive workplace culture and nurture employee loyalty.
On the other hand, if you are in a necessarily conservative industry such as the military equipment manufacturing industry, it is likely also a no brainer that security issues may outweigh any potential benefits. For the many companies in between these two extremes, employee engagement and retention may be one of a number of benefits to consider.
2. CLIENT ENGAGEMENT:
Certain clients in certain industries may have a preference for one type of device over another. If you are visiting a Blackberry dependent tech client in Waterloo, whipping out your iPhone is both rude and stupid. Allowing BYOD flexibility to support various platforms may be essential to reflecting business reality.
3. INCREASED PRODUCTIVITY:
BYOD may positively impact employee productivity. Letting people connect their tablet to the company email and document system may facilitate convenient and more frequent after hours work. Rather than lugging a cumbersome laptop home, employees can use their tablet to finish up a document or clear out their email after the kids go to bed. Business travellers, trade show attendees and salespeople on the road all may find BYOD a critical piece to maintaining productivity out of the office.
Wednesday, April 10, 2013
Top 5 Trends that Impact E-Commerce in 2013
2013 is according to many going to be the year of Mobile commerce, so what does that mean for Online retailers?Let’s take a look at the top 5 trends that will be shaping E-commerce for 2013, and let us see what actions web designers and developers can take to stay on the top of these trends.
1. Localization – Big Opportunities For Small Businesses
Online retailers no more shy away from creating indigenous e-commerce websites. Here we are not referring to merely offering your website in different languages. With going local, we are referring to a totally localized user experience. Thus, expect to see more websites based on traditional design
aesthetics including the use of local color preferences, local language, local offers and essentially local products and services. For small businesses the move is indeed welcomed especially if they cater for niche markets. Ours is a curious generation which loves to explore. The local stuff which is marketed across as traditional and exotic easily attracts customers and generates revenue.
Localization will also pave the way for more personalization whereby users will continue to enjoy an even more one-to-one customer experience. Websites will automatically adapt to show user preferences and tastes. However, personalization will not be only based on past purchases or browsing habits (such as the recommendations offered by Amazon). Instead, we will see more intelligent algorithms that are able to predict which products or service may appeal to you based on advanced segmentation and user profiling.
2. M-Commerce Is The New Buzzword
Online businesses have realized the need for deeper mobile integration. Witness to this is the increased use of responsive web design that dominated 2012. From a user interface perspective, online businesses will continue to adapt to and make the most use of the available screen real estate of the device from which they are being accessed. As such, there will not be one e-commerce site for the desktop and another for the mobile device. Instead, thanks to Responsive Web Design, there will just
Sunday, March 31, 2013
Why FacePhone and FaceDroid will fail
The latest rumours to surface is Facebook releasing its own smartphone..
According to various different reports Facebook will introduce its own version of Android running on a phone with a ton of Facebook features. HTC is on board with Facebook and most likely offer "FaceDroid" on its phones. Facebook is reportidly looking for other manufacturers to join. As for further technical specifications not much is known.
Is this the latest sign of innovation?
Nope, all Android and iOS phones come with Facebook baked into it. Whether it is chat, call, photo, poke or "Like It" it is available.
The Facebook name or brand alone simply is not going to drive people to buy a device based on its brand (Unlike Apple), especially Facebooks' trackrecord with its users privacy is doing the company not any favors.
I just don't see the "FacePhone" on "FaceDroid" being any different from any other current smartphone. Only if Facebook is able to offer something completely new and innovative their FacePhone has a chance to succeed, so a powerfull camera is not going to cut it.
Let me know what you think
Labels:
Android,
Apple,
Facebook,
Facebook Phone Release,
Facebook Smartphone,
FaceDroid,
FacePhone,
HTC One,
Innovation,
IPhone
Sunday, March 24, 2013
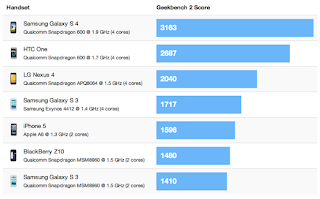
Why IPhone will survive the S4, N4, Z10 and others to come
With the launch of the Samsung Galaxy S4, HTC One, LG Nexus 4 and Blackberry Z10 a war against Apple's IPhone 5 seems to be declared. But is it really? On the surface it might seem this way, but the real motivation could be seen in a different light. That is what I am going to discuss today.
The Blackberry Z10 has a relatively low score, but is basically on par with IPhone 5.
Interestingly enough the Galaxy S3 marginally outperforms the IPhone 5 and the Z10.
Does the IPhone have a future?
The IPhone 5 is far from dead. The results published in the review by Primatelabs need to be looked at with a bit of nuance. The IPhone 5 has been on the market since 6 going 7 months, therefore the comparison with the Galaxy S4, HTC One and LG Nexus 4 are not reflecting its actual capabilities. The S4, One and Nexus 4 all operate on 4 core hardware whilste the 5 is operating on 2 cores (with an operating 2,5 times faster than the IPhone 4S). If you take the release date of the IPhone 5 and benchmark it with phones released in a simular period it suddenly jumps in ranking to #2 behind the Samsung Galaxy S3.
What has the Galaxy S4 to offer that the IPhone 5 has not?
Thursday, March 14, 2013
5 Reasons Why Chrome OS fusing with Android is Good!
My previous posts were mostly about security concern and the rise of wearable devices.
In this post I discuss a "minor" staff change at Google and how it relates to the Android OS and why it can be seen as sign of strategic change in Google's approach
This week saw Google reveals its future mobile ambitions by replacing long serving Andy Rubin (head of Google Mobile Android Division since 2004) by Sundar Pinchai, who is currently head of Google Chrome's department and has been responsible for the browsers' meteoric rise in the last 4 years.
In practice this means that Mr. Pinchai will be heading both Google Chrome and Google Apps. Losely translating this means that Chrome will is preparing for the moment that Android (Mobile Devices) and Chrome (PC/Desktop) will become one.
1. What is Google aiming for?
At current Google is not charging any of the companies deploying Andriod in Mobile Devices. Instead Google is earning on the applications that run on Andriod via its Play Store. Google is making money with the Advertising campaigns targeting Andriod. By merging Andriod OS and Chrome OS Google creates a potentially massive new revenue base.
2. What did the "Chromebook Pixel" do?
The release of Google's "Chromebook Pixel" laptop, which provides a superb browsing experience and native intergration with Google's Cloud Service, demonstrated its inability too rival both the Windows and MAC Operating Systems. Basically all that you expect from a cheap laptop
As reviews showed: it was not a greatly celebrated success and that is an understatement. But not to fear, Google is here. Turning a bad experience into a usefull one!
3. What makes Android so interesting?
In this post I discuss a "minor" staff change at Google and how it relates to the Android OS and why it can be seen as sign of strategic change in Google's approach
This week saw Google reveals its future mobile ambitions by replacing long serving Andy Rubin (head of Google Mobile Android Division since 2004) by Sundar Pinchai, who is currently head of Google Chrome's department and has been responsible for the browsers' meteoric rise in the last 4 years.
In practice this means that Mr. Pinchai will be heading both Google Chrome and Google Apps. Losely translating this means that Chrome will is preparing for the moment that Android (Mobile Devices) and Chrome (PC/Desktop) will become one.
1. What is Google aiming for?
At current Google is not charging any of the companies deploying Andriod in Mobile Devices. Instead Google is earning on the applications that run on Andriod via its Play Store. Google is making money with the Advertising campaigns targeting Andriod. By merging Andriod OS and Chrome OS Google creates a potentially massive new revenue base.
2. What did the "Chromebook Pixel" do?
The release of Google's "Chromebook Pixel" laptop, which provides a superb browsing experience and native intergration with Google's Cloud Service, demonstrated its inability too rival both the Windows and MAC Operating Systems. Basically all that you expect from a cheap laptop
As reviews showed: it was not a greatly celebrated success and that is an understatement. But not to fear, Google is here. Turning a bad experience into a usefull one!
3. What makes Android so interesting?
Saturday, March 9, 2013
6 Smart Watches to keep your eye on!
Both link in well with their end-users and operate on sophisticated technology to operate and synchronize with your mobile devices.
The future has more in store for us, with the highly anticipated releases of Apple's
I-Watch and Google's Project Glass.
In this blog I want to do something else. Listed are 6 wearable (why do I want say portable) devices and I would like you to rate them! Simple, fun and not too exhausting.
I am not affiliated to any of the producers of these products, so I don't make any money out of it.
The best known wearable computing devices at the moment are:
1.Lark Watch: This device awakens sleepers quietly and gently. It measures and analyzes the user’s sleep, evaluates sleep patterns with assessments, and coaches users about how to improve their sleep experience based on their sleep type.
3.I’m Watch: The first smartwatch — has everything your smartphone has. The I’M Watch has a 1.55-inch touch screen, Bluetooth tethering, and a 4GB memory card. The graphical user interface is minimal, clean, user friendly, and iPhone (plus other smartphones) compatible. High-resolution display has water resistant surface and screen similar to the iPod nano.
Tuesday, March 5, 2013
Marketeers wake up! MMS/SMS campaign is the most effective way!
 |
| image: besttextmarketing.com |
Most marketing people try to convince me that SMS marketing is dead, not done, to complicated, to many regulations. I don't agree.
Where SMS Messaging is becoming pretty much the 1980's typewriter vs Commador 64, MMS offers exactly the same service only it is empowered by the Graphical User Interface on almost all mobile devices and increasing volumes of mobile user. This makes MMS perfect to market anything! It actually makes a marketeer's job easier! MMS enables you to add pictures and videos of products and services.
A 2009 study on marketings techniques concluded that:
"Mobile text messaging, the same 160-character dispatches first popularized by nimble-fingered teenagers, may be the closest thing in the information-overloaded digital marketing world to a guaranteed read."Some simple stats prove the point:
1. 97% of all marketing messages are opened (email marketing dreams of that rate)
2. 83% of all marketing messages are opened within 60 minutes of receiving
3. 95% of opted into a text message opened and read within 3 minutes
I am no super marketeer, nor a wizz kid, but 95% is fantastic rate, if only 95% of my page hits would read my blog... I would be bathing in internet sunshine.
MMS is basically created the likes of Instagram and Pinterest, where would they be without graphics uploaded directly from mobile devices?
When it comes to SMS and MMS marketing we all have experience with these dreaded messages making us think our phones are infected with "Mobile Herpes", but those are bad industry practices. In fact SMS/MMS Marketing is highly regulated (especially in the US).
As long as you stay within the rules of the law MMS offers M-Commerce an unbelievable platform.
Want to know more? Go to this section of my blog to download it or get "The 2013 Guide to TXT messaging regulations & best practices" here by Mogreet
Thanks for reading again, PLEASE LEAVE YOUR COMMENTS! I really like to hear what you have to say about it!
Monday, March 4, 2013
5 Basics Principles To Enter M-Commerce
All jokes aside. I have now aquired my own webdomains, going through SEO, affiliate marketing (what a lot of garbage in that section), Analysis etc.
Suddenly I realized that by doing so I almost overlooked my check-list of basics I put together a couple of weeks ago.
Because you insist I'll share them with you
5 Basics to enter M-Commerce:
Subscribe to:
Comments (Atom)